Madan Belbase
Published: Mar 2026
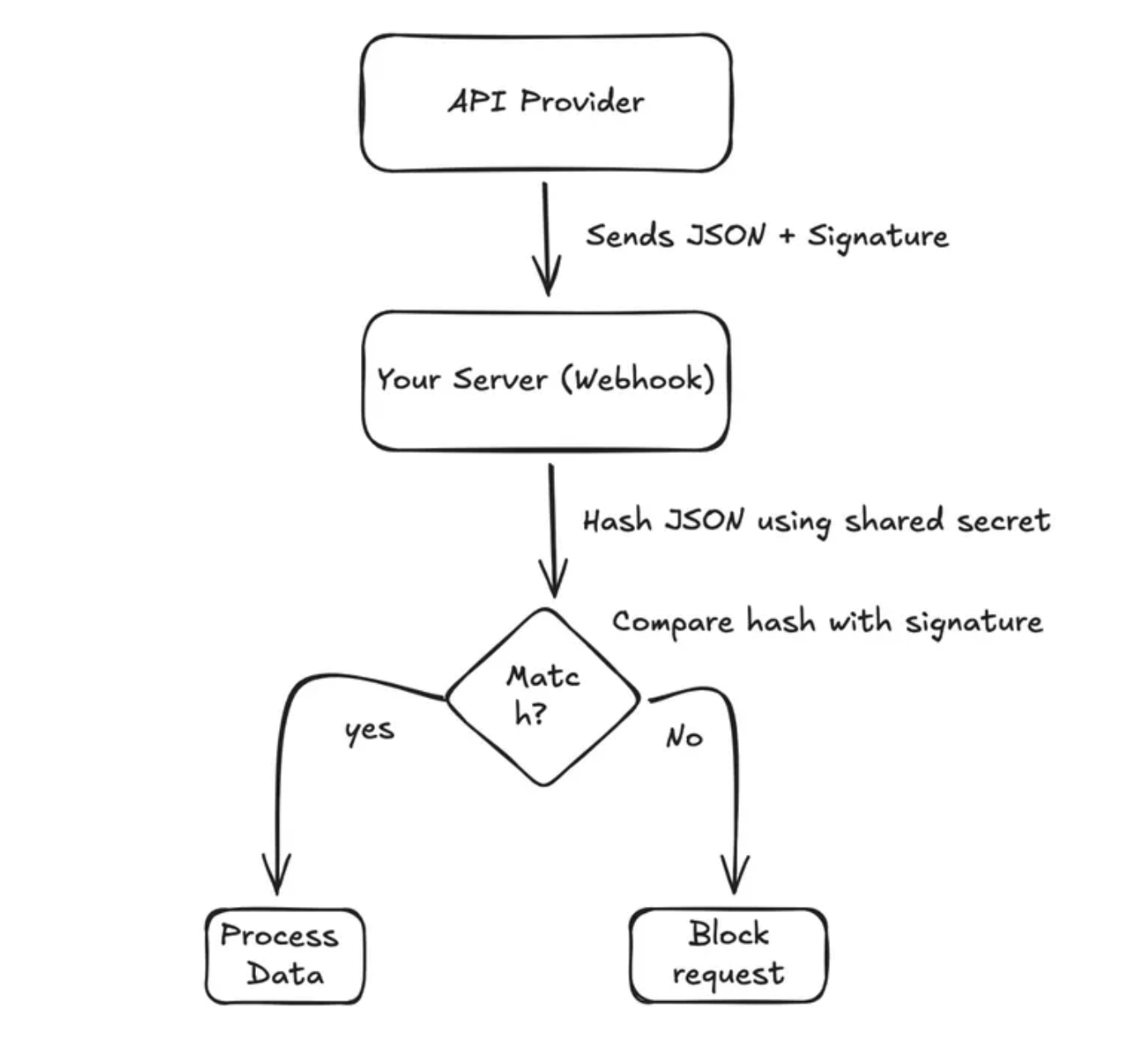
Webhook Security – Don’t Let Hackers Spoof Your Data
Learn the best practices for securing webhooks and preventing malicious data injection into your systems.
$ read --full-articleBuilding scalable systems and efficient architectures. Passionate about clean code and performance optimization.
{
"name": "Madan Belbase",
"role": "Computer Engineering Student",
"focus": [
"Backend Development",
"System Design"
],
"skills": {
"technical": [
"Node.js",
"API",
"Database Design"
],
"soft": [
"Leadership",
"Problem Solving",
"Collaboration"
]
}
}| INSTITUTION | DEGREE | YEAR |
|---|---|---|
| Nepal College of IT | B.E. Computer | 2023-Present |
| Morgan Int'l College | +2 Science | 2021-2023 |
| Shree Devi Prabhav | SEE | 2010-2020 |
Runtime Environment
Programming Language
Scripting & Automation
Frontend Library
NoSQL Database
Cloud Services
Version Control
Educational platform UI


A full-stack web application that allows users to swap, request, and manage time slots seamlessly.
Modern responsive portfolio
Under development
Madan Belbase
Published: Mar 2026
Learn the best practices for securing webhooks and preventing malicious data injection into your systems.
$ read --full-article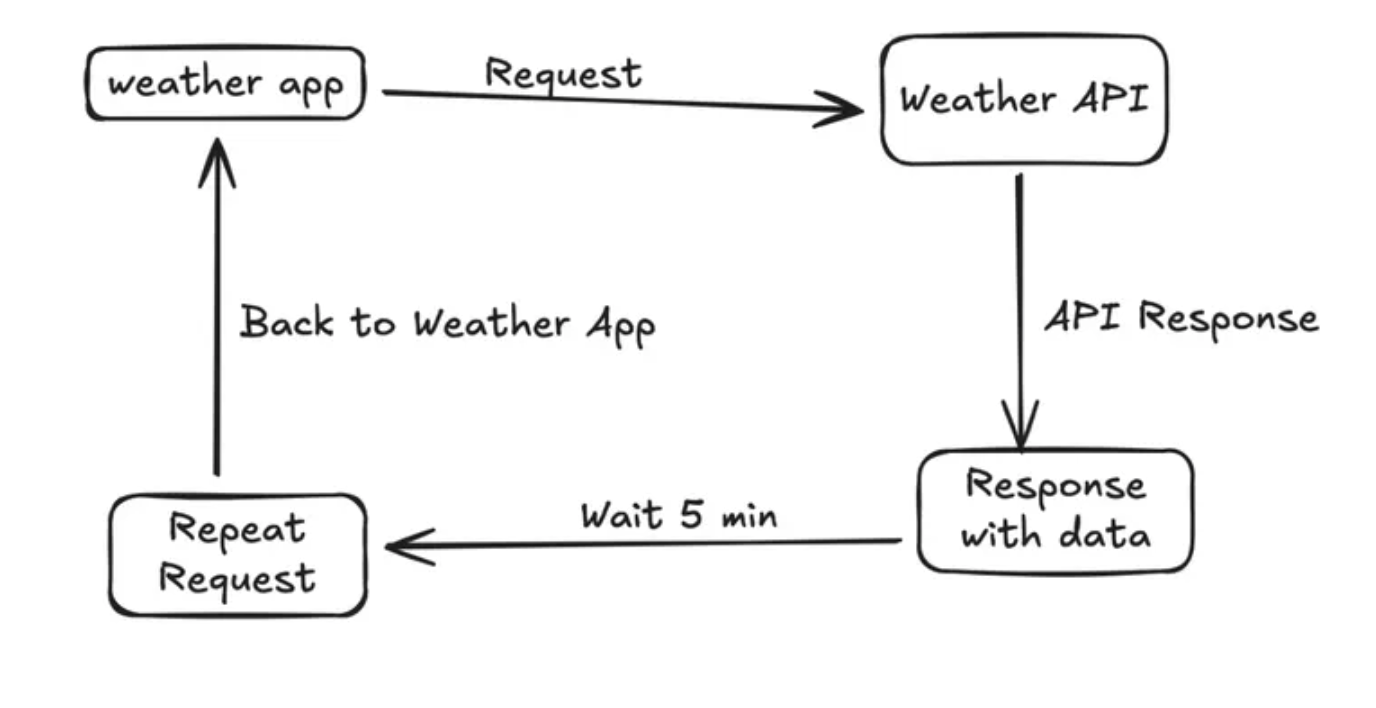
Madan Belbase
Published: Mar 2026
How Webhooks Solve the Polling Problem and improve system efficiency.
$ read --full-article
Madan Belbase
Published: Mar 2026
When the API Sends Unexpected Data – and how Zod fixes it.
$ read --full-articleconsole.log("Let's connect! Reach out via email or social media.")